Enable Microsoft Entra ID (Azure AD) SSO and MFA to Oracle Siebel via Datawiza
Overview
This tutorial shows how to enable Microsoft Entra ID (Azure AD) SSO and MFA for Oracle Siebel via Datawiza. Learn more about enabling SSO and MFA for Oracle Siebel with Datawiza.
The benefits of integrating applications with Microsoft Entra ID via Datawiza includes:
- Improved Zero Trust security through Microsoft Entra ID, MFA and Conditional Access.
- No-Code easy integration between Microsoft Entra ID and any web applications, including Oracle JD Edwards, E-Business Suite, Siebel, Peoplesoft and homegrown apps.
- A single control plane, Datawiza Cloud Manage Console, to manage access to applications in public clouds and on-premise.
Background
This document focuses on Oracle Siebel application integration using HTTP header-based authentication to manage access to protected resources.
For legacy applications, due to the absence of modern SSO protocol (SAML or OIDC) support, a direct integration with a modern Identity Provider is difficult. Datawiza Access Proxy bridges the gap between the legacy application and the modern identity provider, through protocol transitioning. Datawiza Access Proxy lowers integration overhead, saves engineering time, and improves application security.
Architecture
The solution contains the following components:
- Microsoft Entra ID: Microsoft's cloud-based identity and access management service, which helps users sign in and access external and internal resources.
- Oracle Siebel Application: the legacy application to be protected by Microsoft Entra ID and Datawiza.
- Datawiza Access Proxy (DAP): A lightweight container-based reverse-proxy implements OIDC or SAML protocol for user sign-on flow and transparently passes identity to applications through HTTP headers.
- Datawiza Cloud Management Console (DCMC): A centralized management console that manages DAP. DCMC provides UI and RESTful APIs for administrators to manage the configurations of DAP and its granular access control policies.
Steps Description
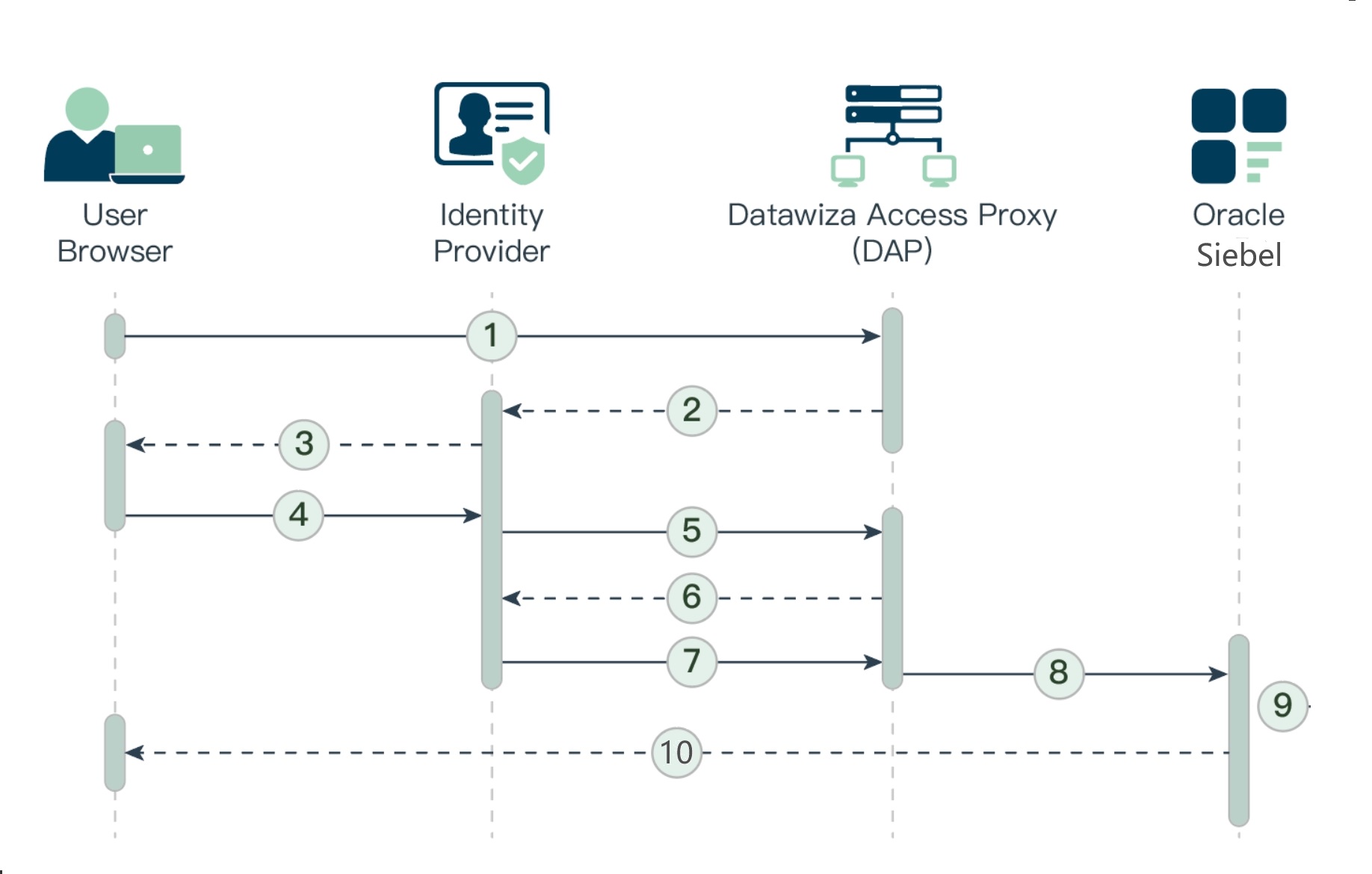
- The user requests access to a DAP-protected Siebel resource.
- DAP redirects the user's browser to the identity provider (e.g.,Microsoft Entra ID, Okta, Ping or others).
- Identity Provider presents its login page to the user.
- The user submits their credentials to the identity provider.
- Upon successful authentication, the identity provider redirects the user's browser to DAP.
- DAP communicates with the identity provider to exchange tokens.
- Identity Provider issues the user's username and relative information to DAP.
- DAP sets an HTTP header variable that maps to the Siebel user ID, and passes the authenticated user's username in the header variable to the Siebel Application Interface.
- The Siebel Application Interface passes the authenticated user's user name and the value for the Trust Token parameter to the security adapter. Then the security adapter compares the Trust Token value, if the values match, then the Application Object Manager accepts the request.
- The Application Object Manager uses the returned token to retrieve the user's data based on their roles and visibility. If the user is not authorized, the user is denied access and redirected to another URL as determined by the organization's administrator. Otherwise, it presents the requested protected resource to the user.
Prerequisites
Prior Datawiza Access Proxy experience isn't necessary, but you need:
- An Azure subscription. If you don't have a subscription, you can get a trial account.
- An Microsoft Entra ID tenant that's linked to your Azure subscription.
- Docker and docker-compose are required to run DAP.
- User identities synchronized from an on-premises directory to Microsoft Entra ID or created directly within Microsoft Entra ID and flowed back to your on-premises directory.
- An account with Microsoft Entra ID application admin permissions.
- An existing Oracle Siebel environment and LDAP Security Adapter is installed on and enabled.
Getting started with DAP
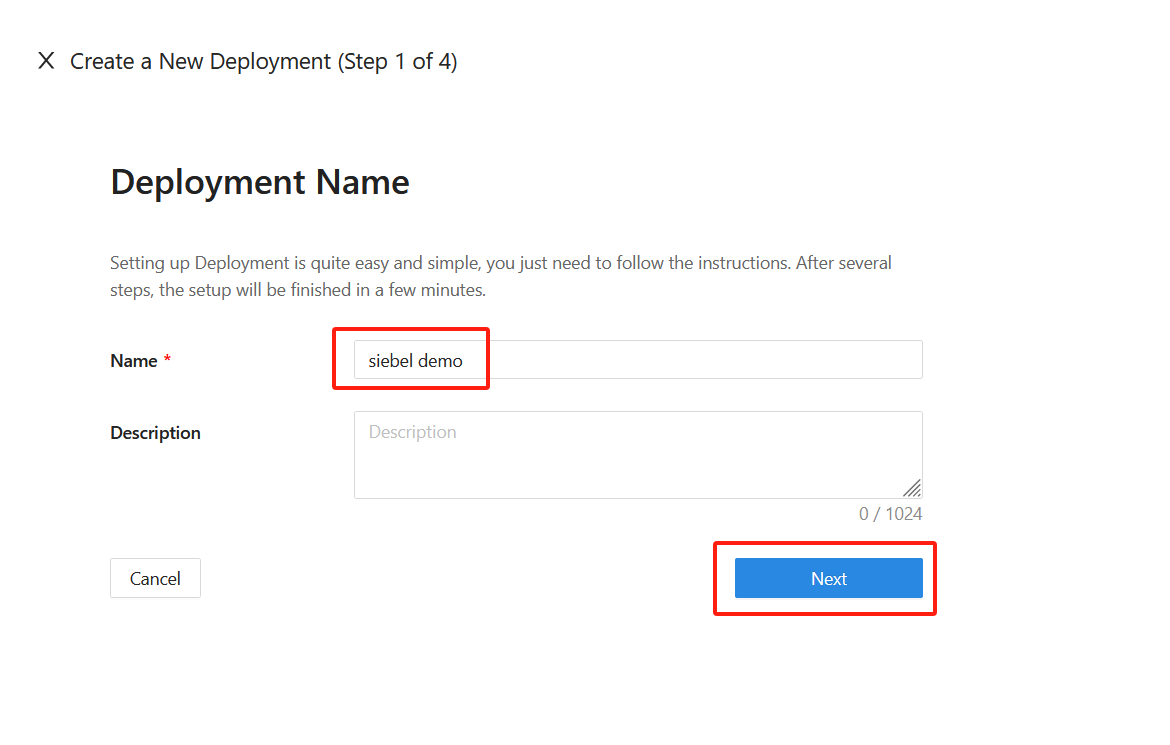
To integrate Oracle Siebel with Microsoft Entra ID:
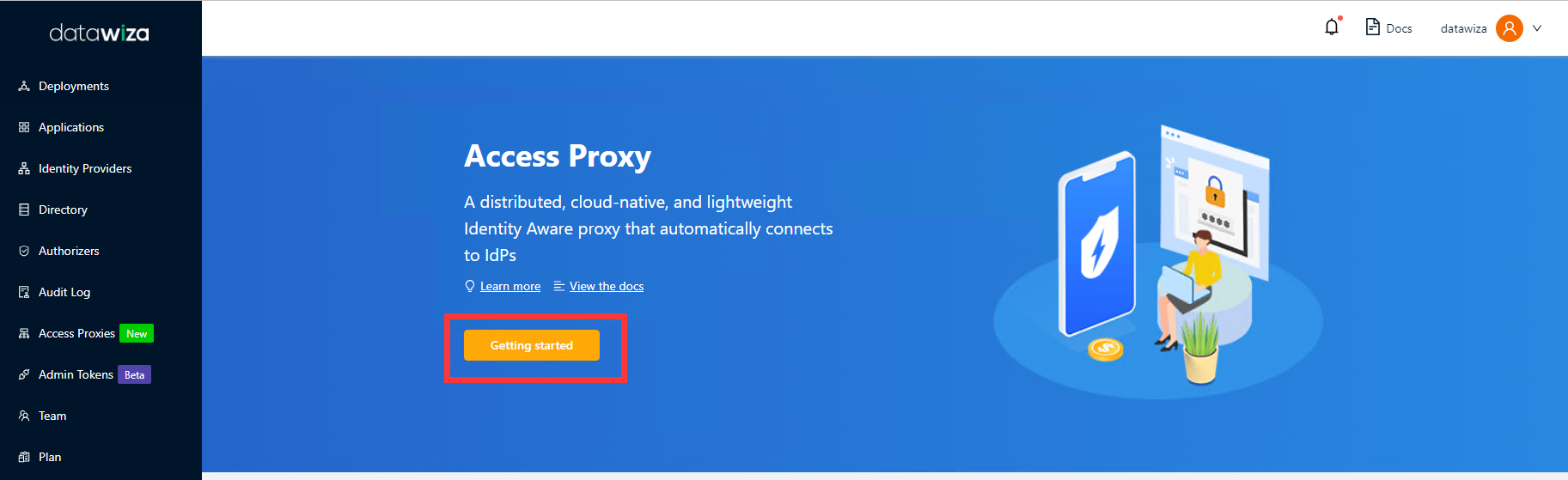
Sign in to Datawiza Cloud Management Console.
The Welcome page appears.
Select the orange Getting started button.
In the Name and Description fields, enter the relevant information.
Select Next.
On the Add Application dialog, use the following values:
Property Value Platform Web App Name Enter a unique application name. Public Domain For example: https://siebel.example.com. For testing, you can use localhost DNS. If you aren't deploying DAP behind a load balancer, use the Public Domain with the port.SSL Check the Enable SSL and use datawiza self-signed certificate checkbox for testing if you are using SSL. For production, you can upload your own certificates. Listen Port The port that DAP listens on. I use 443. Upstream Servers The Oracle Siebel implementation URL and port to be protected. 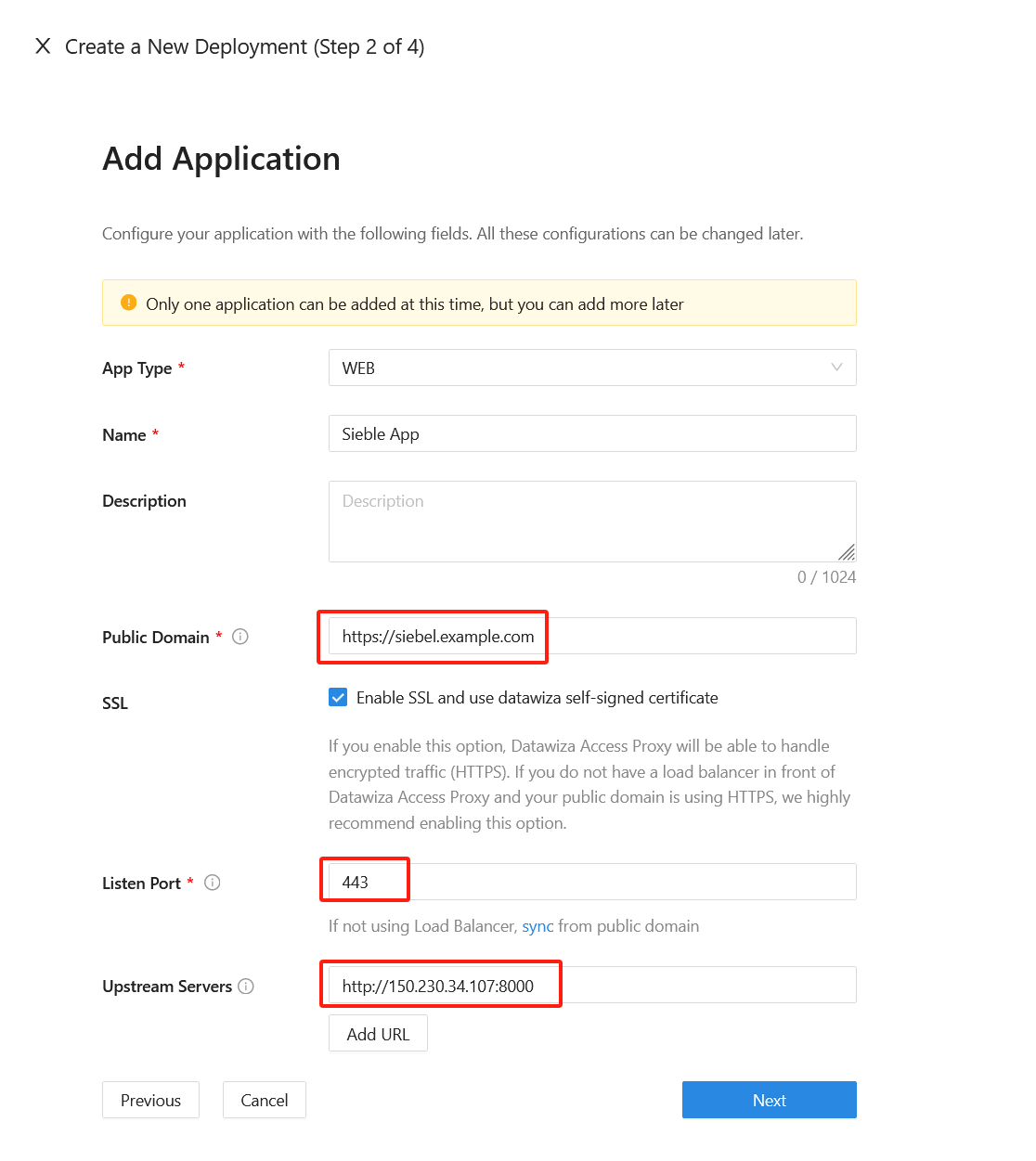
Select Next.
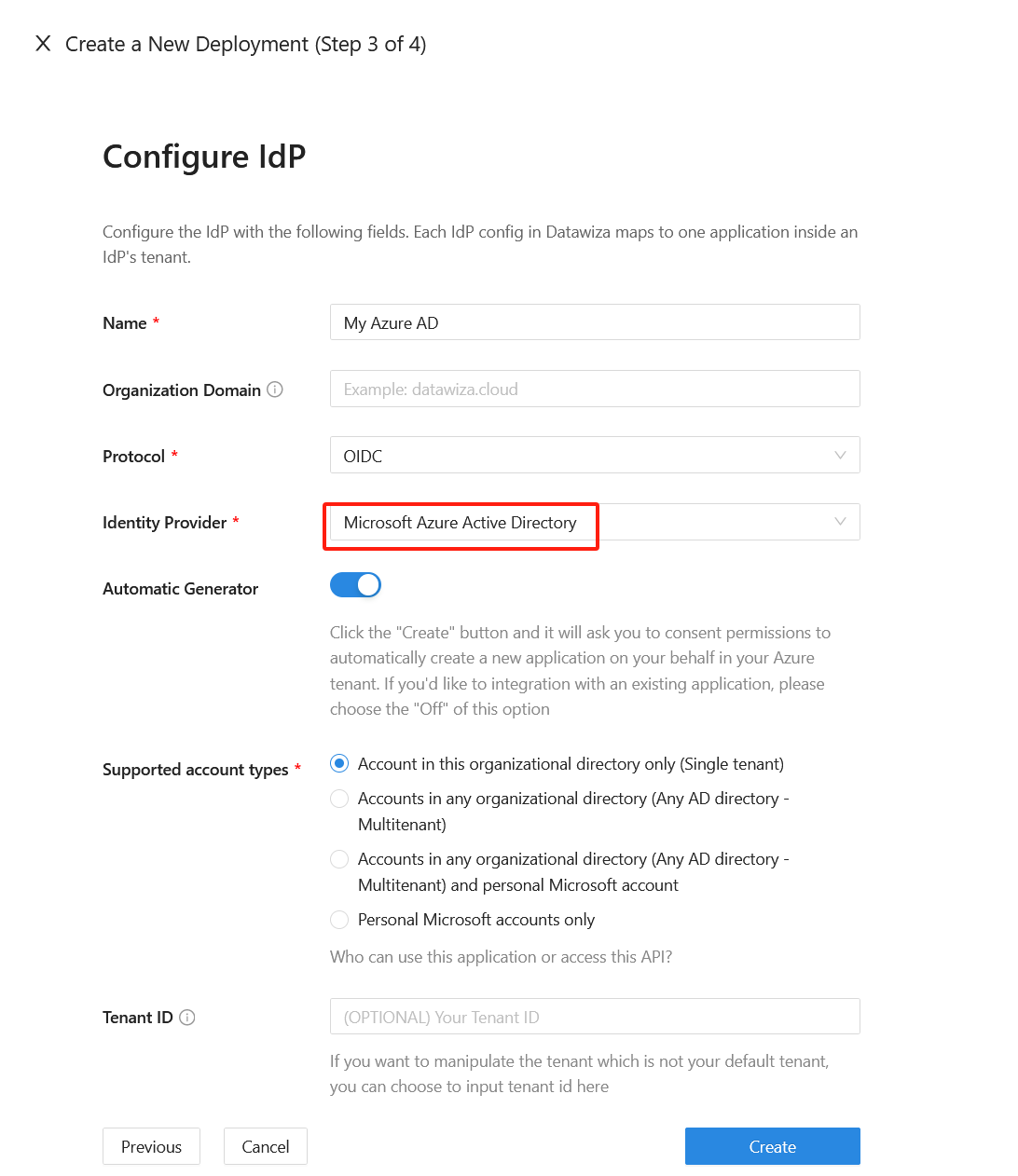
On the Configure IdP dialog, enter the relevant information.
Info
DCMC has one-click integration to help complete Microsoft Entra ID configuration. DCMC calls the Microsoft Graph API to create an application registration on your behalf in your Microsoft Entra ID tenant.
Select Create.
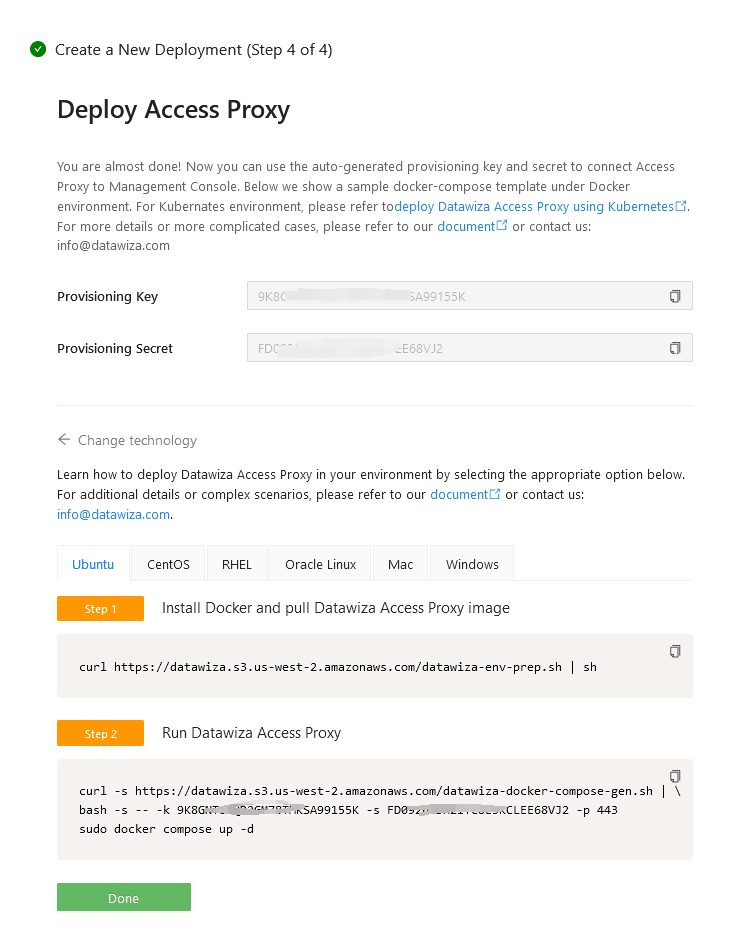
Install and run Datawiza Access Proxy
Once clicking on the Create button, the basic configuration on the management console is finished. You will see the final step of the guide, which presents you with a page showing the simple steps to deploy Datawiza Access Proxy (DAP) with your application. Note down the commands for your deployment. The first command will download Docker and Datawiza Access Proxy image, and the second command will create a Docker Compose file and run Datawiza Access Proxy. You can refer to Install and Run Datawiza Access Proxy by command for more information.
SSO and HTTP headers
The DAP gets user attributes from IdP and passes them to the upstream application via header or cookie.
For the Oracle Siebel application to recognize the user correctly, there's another configuration step. Using a certain name, it instructs DAP to pass the values from the IdP to the application through the HTTP header.
Such configuration will be done in the Applications tab on the left panel and go to Attribute Pass sub-tab. For Oracle Siebel, please refer to the screenshot below to configure the attribute pass:
| Property | Value |
|---|---|
| Field | |
| Expected | SSO_SIEBEL_USER |
| Type | Header |
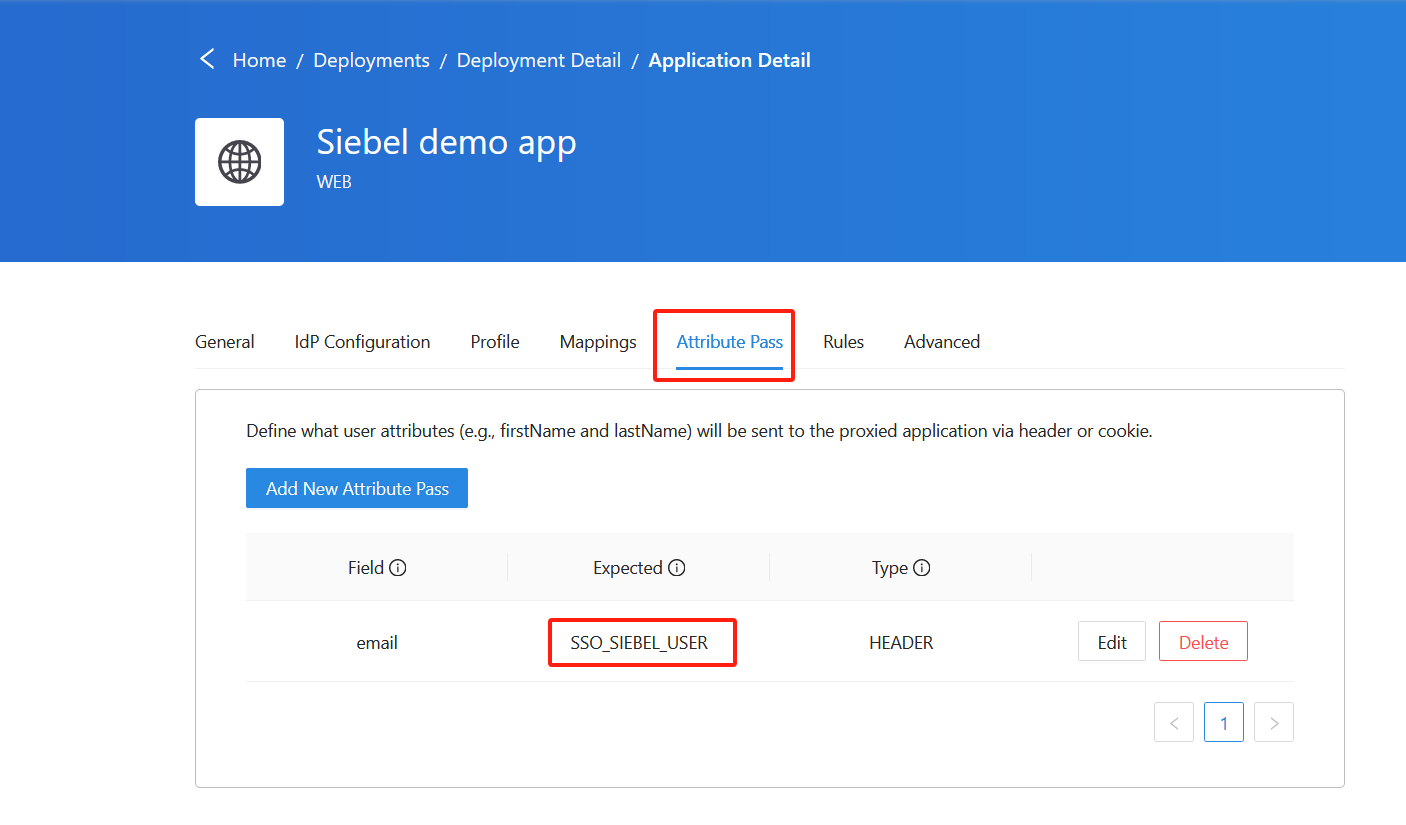
Info
In this setup, the mapping between the email and SSO_SIEBEL_USER serves as an example. You have the flexibility to modify this configuration by either adjusting the Field or altering the attribute mapping within the Mappings sub-tab.
(Optional) SSL Configuration
- By default, when you set up this application, it will use the Datawiza self-sign certificate, but you still have the chance to replace it with your own certificate. Select the Advanced tab. Click the edit button, then upload your own certificate.
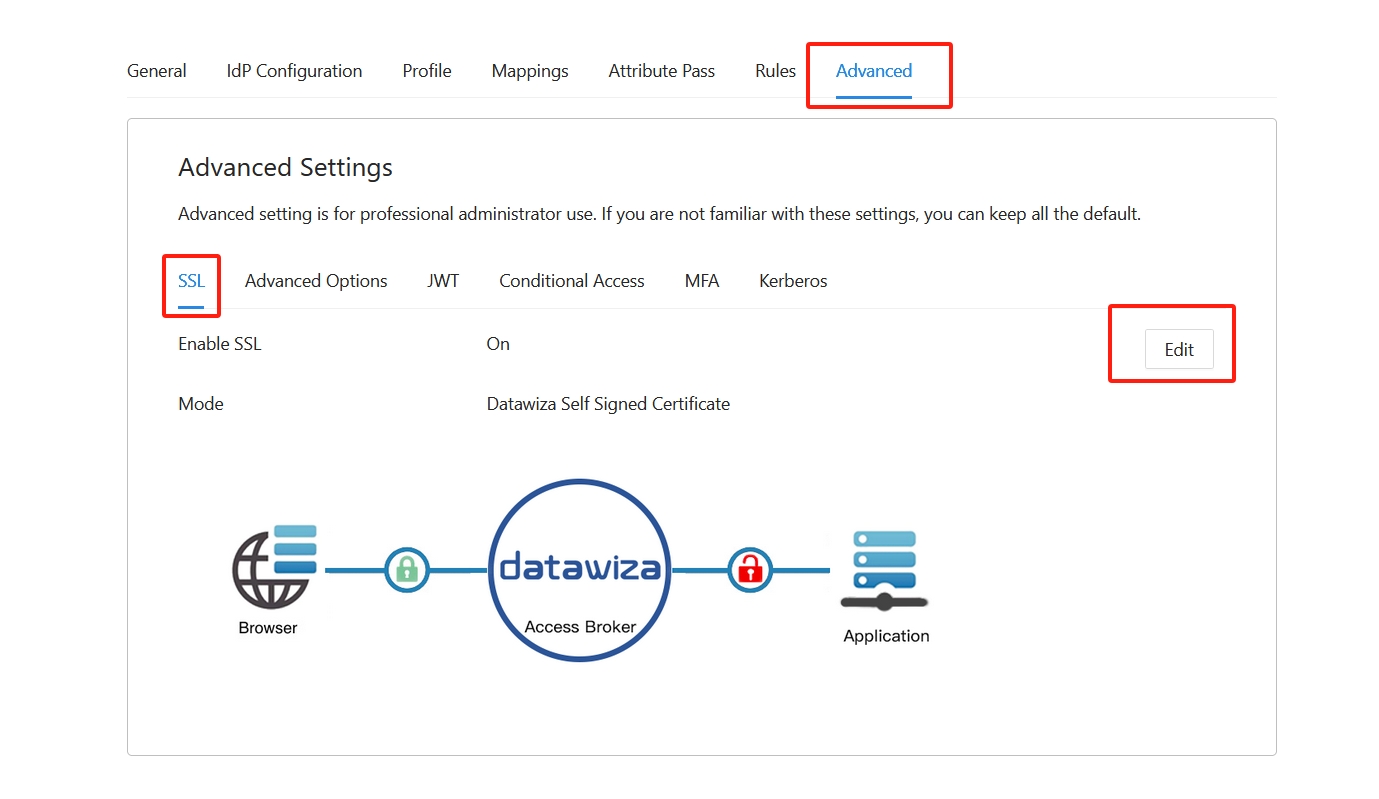
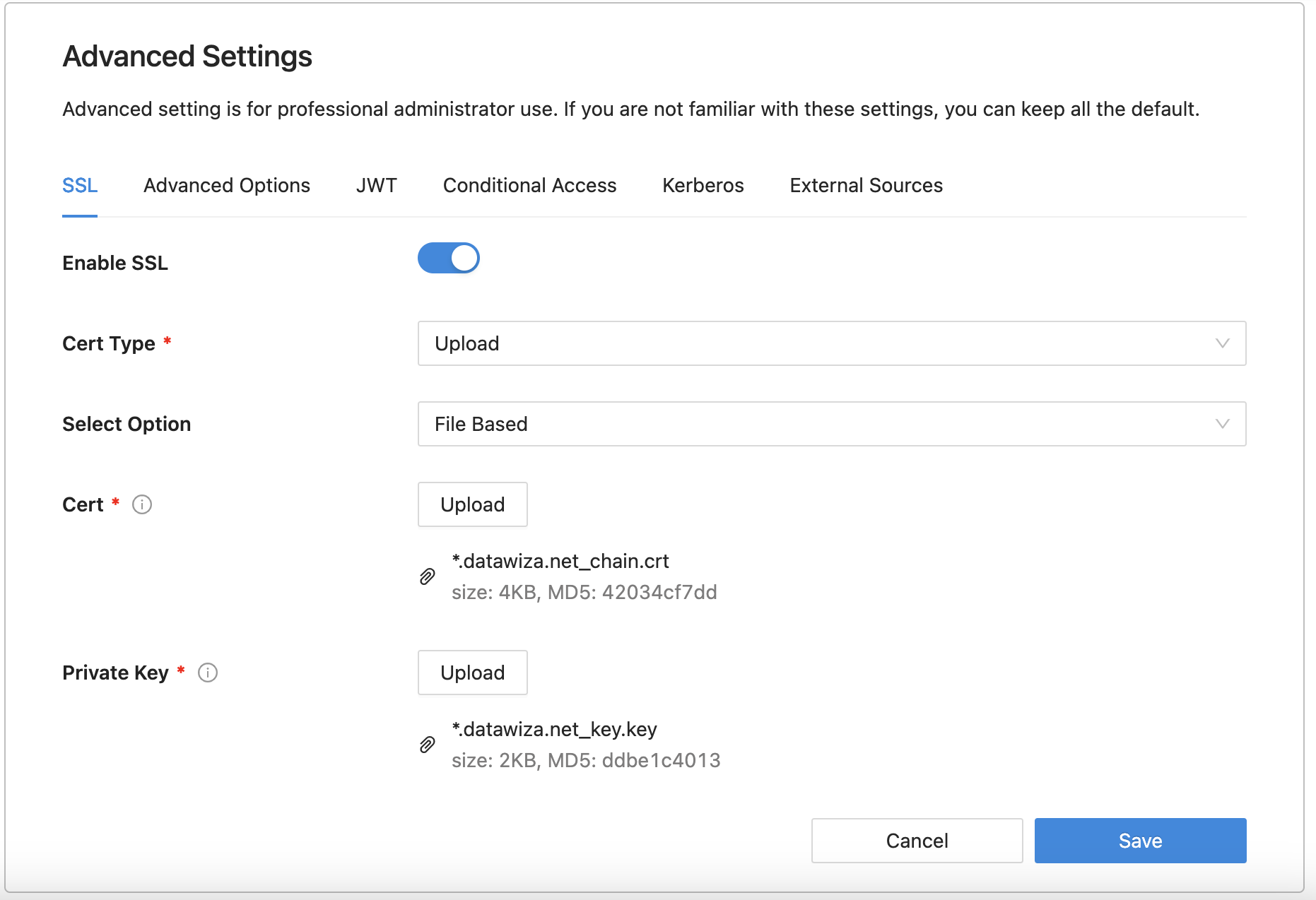
- Select Save.
Enable SSO in the Oracle Siebel Portal
To enable header-based authentication SSO in the Oracle Siebel environment:
Make sure that Siebel application is set up for using LDAP or ADSI security adapter.
Confirm if Siebel application is working effectively with LDAP or ADSI authentication using LDAPSecAdpt or ADSISecAdpt profile.
Logon to Oracle Siebel Portal:
http://{your-siebel-fqdn}:{port}/siebel/smc/index.htmlusing Admin credentials.Enable Single Sign On for the LDAPSecAdpt Profile by going to Profiles >> Security >> LDAP Datasource and update the below parameters:
- Configure Web SingleSignOn -- True
- Trust Token -- Welcome1
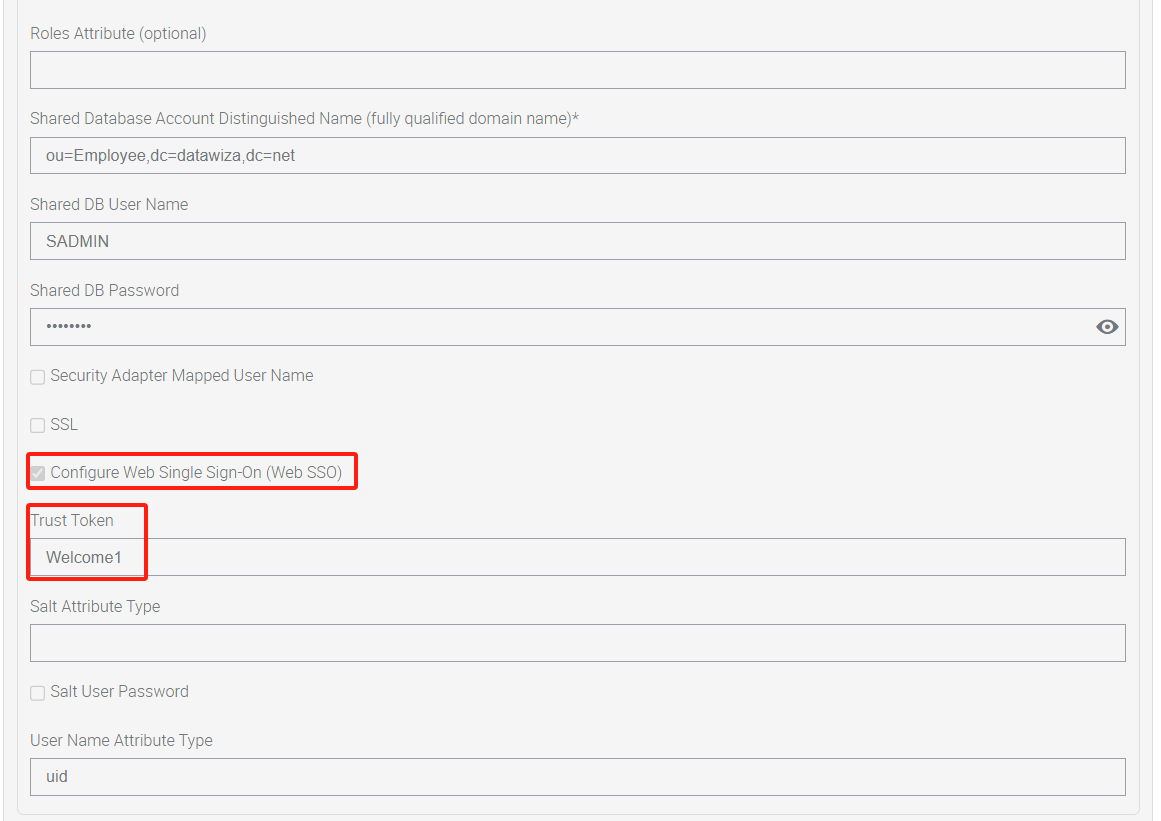 For older versions of Siebel, your may need to edit through Server Component Parameter by going to Site Map >> Administration - Server Configuration >> Profile Configuration and update the below parameters:
For older versions of Siebel, your may need to edit through Server Component Parameter by going to Site Map >> Administration - Server Configuration >> Profile Configuration and update the below parameters: 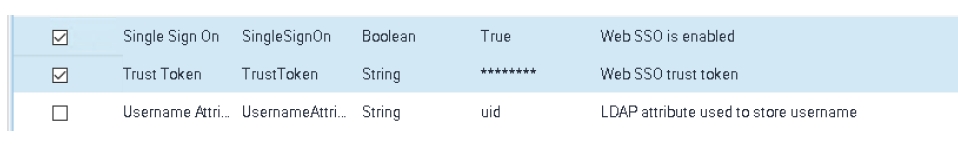
Go to Siebel Deployment >> Profiles >> Application Interface (AI) profile and select the profile and click on Edit button to edit the profile.
In Edit Profile, go to Applications and narrow down on the fins (enu) and expand Enhanced Authentication and check Configure Web Single Sign On checkbox and input Trust Token with the same as before:
Welcome1. Then input User Specification as SSO_SIEBEL_USER.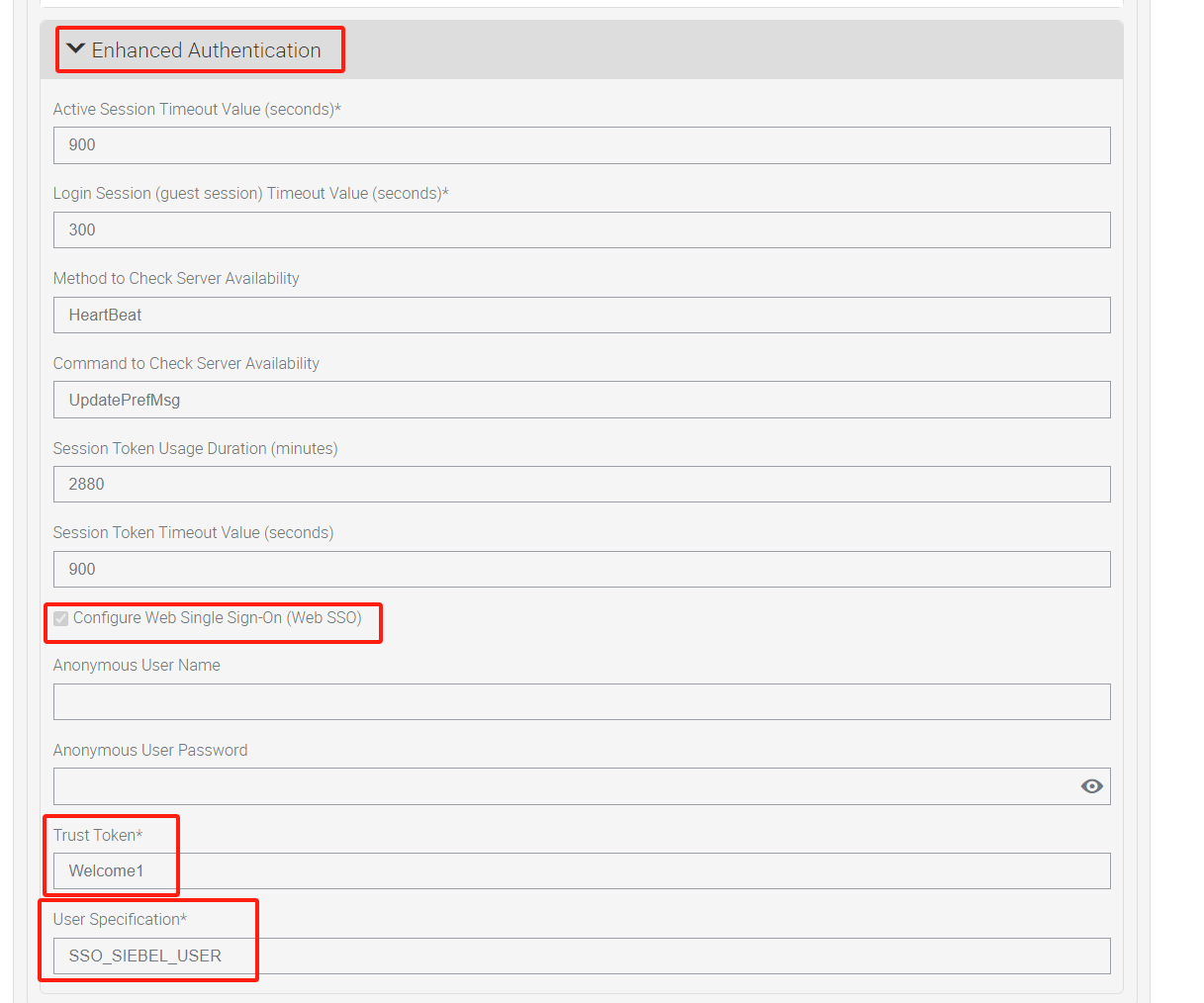 For older versions of Siebel, you may need to edit it through eapps.cfg file. The following sample is an example:
For older versions of Siebel, you may need to edit it through eapps.cfg file. The following sample is an example:
[/prmportal_enu_sso]
SingleSignOn = TRUE
TrustToken = Welcome1
UserSpec = SSO_SIEBEL_USER
UserSpecSource = Header
- Restart the Siebel server, Application Interface (AI) Application Container, Siebel Enterprise Server (SES) Application Container and Gateway server for changes to take effect.
Test an Oracle Siebel application
To confirm SSO and MFA for Oracle Siebel application work correctly, access the new Siebel URL https://siebel.example.com in the browser. A prompt should appear to use an Identity Provider account for signing in. Credentials and optional MFA are checked and the Oracle Siebel home page appears.
Note
For security purpose, organizations using this model in production environment should block all direct access to the application, thus forcing the use of a strict path through the Datawiza Access Proxy.
